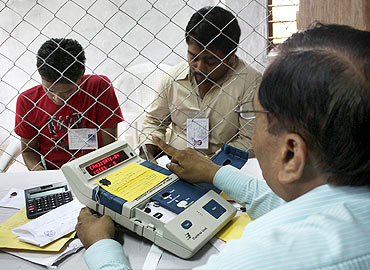
Photographs: Punit Paranjpe/Reuters
J Alex Halderman, leading electronic voting security expert tells rediff.com's Vicky Nanjappa what the problems with India's voting machines are and how to fix them
The arrest and the subsequent release on bail of e-voting researcher Hari Prasad has opened a Pandora box regarding India's Electronic Voting Machines. India's Election Commission, the researchers said, was reluctant to come forward and debate the issue, prompting them to dermonstrate how the machines could be tampered with.
Halderman, assistant professor of electrical engineering and computer science,at the University of Michigan, who has worked along with Hari Prasad in exposing the flaws in this machine, says they are extremely vulnerable.
Could you explain to us how an EVM can be tampered with?
Far from being 'tamper proof', EVMs are vulnerable to most of the same security problems as the paper ballot boxes they replaced, including an electronic form of booth capturing. Furthermore, unlike the old paper ballot boxes, EVMs can be tampered with long before elections take place to cause fraudulent results months or years later.
The methods of tampering we uncovered fall into three categories. The first category is that dishonest insiders or other criminals can manipulate the EVM to change the votes stored inside. This could happen during polling or in the time between polling and counting. One way to do this involves attaching an electronic device to the memory chips inside the machine, which holds the digital record of each vote. This device could then rewrite the vote data to favour a given candidate. We created such a device to demonstrate how easy this manipulation could be: a criminal could just open the EVM and clip the tiny device to the memory chips in a moment.
Memory manipulator devices could also be used for booth capturing, because they bypass the EVM's ability to control how quickly votes are cast. Not only is the device we demonstrated discreet and simple to use, but also cheap enough for a criminal to hand out to a squad of goons.
'Anyone with an electronics background could hack an EVM'
Image: People stand in a queue to cast votes outside a polling centre in MumbaiPhotographs: Punit Paranjpe/Reuters
Can EVMs be rigged a long time in advance or is it done just before the elections?
That brings us to the other two categories of tampering that we found. The second category of tampering is that criminals could replace parts of the EVMs (or even whole machines) with look-alikes that behave dishonestly. This would allow criminals to tamper with machines while they are in storage and rig them to cheat in future elections. Many parts of the system could be replaced, but our study focussed on the LED display -- a small circuit inside the machine that is used during counting to indicate how many votes each candidate received. As a demonstration, we built a dishonest display that looks just like the real one but contains a hidden chip that substitutes fraudulent vote totals. Look-alike displays can be installed with only brief physical access to the machines. The usual pre-election mock polls wouldn't catch this cheating, because the display only cheats after hundreds of votes are cast.
Such attacks might seem high tech, but they're straightforward for anyone with an electronics background. One of my students built our first dishonest display in less than five days. India has no shortage of skilled electrical engineers who would need even less time.
The third category, and perhaps most worrying, has to do with the software, which controls almost all aspects of the EVM's functioning. EC expert committee chairman P V Indiresan has said that only 3 to 4 junior officials at the EVM manufacturers know what is in the software code, and that even he and the EC have never seen it. If some of these officials are dishonest, they could add a 'back door' to the code that would steal votes upon receiving a secret combination of key presses or other signal. The back door would then be built into every EVM that is manufactured.
Dishonest officials would face a low risk of being caught, because the EVM design makes it extremely hard for anyone, even the EC, to read or inspect the software once the machines are assembled. Perhaps these officials are honest, but voters have no choice except to trust them. If some of these junior officials at the EVM manufacturers are dishonest, they can compromise the entire national election system.
Some of the tampering methods our study describes require physical access to the machines, but insiders regularly have such access when the machines are in storage and during routine maintenance. Others might be able to get access in places where machines are stored with lax security. There is well-documented precedent for these kinds of attacks in a similar security-critical technology: casino gambling machines. Despite sophisticated security controls and intensive government oversight, there have been many cases in the US where gambling machines have been electronically rigged, most often by dishonest insiders at the companies that manufactured and serviced them.
'Mobile phones can be used to tamper with EVMs'
Image: An election official prepares to count ballots inside a counting centre in Gandhinagar, GujaratPhotographs: Amit Dave/Reuters
Since the order of the candidates on the ballot isn't known until shortly before voting, the criminals would need some way to later signal to the machines which ballot position should receive stolen votes. One way they could do this is by installing a radio receiver in the EVM. We demonstrated this by adding a hidden Bluetooth radio chip to the dishonest display we built. If this display was installed in an EVM, a nearby criminal could select the winning candidate using a mobile phone.
Do you have any material to show that the machines used in Indian elections were rigged?
Our study does not even attempt to establish that any past election was stolen. Nobody can reasonably claim, based solely on the results we have published, that an election result now settled should be overturned. Proving actual fraud would require more evidence and a different kind of investigation.
'Indian EVMs have never been independently audited'
Image: A scene inside a counting centre during the last elections. A file picturePhotographs: Amit Dave/Reuters
Hari Prasad asked Rop Gonggrijp and me to participate in the study because we are established researchers in the electronic voting security field. Rop lives in the Netherlands, and he discovered serious security problems in EVMs used there. This led his country to switch back to paper ballots.
I co-authored the first academic security analysis of a deployed electronic voting machine. Since then I have co-authored security reviews that found flaws in many other kinds of EVMs, including a state-wide voting system review commissioned by the California government.
Rop and me agreed to help study the Indian EVMs out of scientific curiosity, and because we believe voting security is of fundamental importance to all democracies. The EVMs have an unusual design, but the EC has never permitted Indian researchers or anybody else to complete a rigorous, independent security evaluation.
In cases around the world, every time a manufacturer or government maintained that an EVM was fully secure without allowing independent scientific review, there turned out to be serious undisclosed weaknesses.
' The EC's allegations are counterproductive'
Image: Election officials carry electronic voting machines for counting in AllahabadPhotographs: Jitendra Prakash/Reuters
These allegations are completely baseless and counterproductive. We have long track records independently analyzing voting machine security, and all our past work is easy to find on the Internet. Our participation was paid for entirely from our university or personal funds, except for the cost of our travel to India, which was arranged by a citizens' group named Save Indian Democracy.
Allegations like these are counterproductive because they are a distraction from the very real problems that our study with Hari Prasad found. Our team has documented these vulnerabilities in a peer-reviewed scientific paper that will be published this October at a leading computer security research conference in Chicago.
The paper is available online at IndiaEVM.org, and I hope people will read it and decide for themselves whether the problems should be taken seriously.
'The EC must seek help from India's techies'
Image: Jubilant Congress workers after the last General Elections victory.Photographs: Punit Paranjpe/Reuters
Do you see a political conspiracy in the Hari Prasad case?
What happened to Hari Prasad is extremely troubling. The arresting officers told him they were acting under 'pressure from the top', and the circumstances strongly suggest that this was more than a routine investigation.
The case against Hari Prasad is all the more troubling because it distracts from the primary problem: India's electronic voting machines have fundamental security flaws, and do not provide the transparency necessary for voters to have confidence in elections.
To fix these problems, the Election Commission will need help from India's technical community. Arresting and interrogating a key member of that community is enormously counterproductive.
'India should return to the paper ballot'
Image: Election officials handover EVMs to the returning officer in LehPhotographs: Amit Gupta/Reuters
The fundamental problem with paperless EVMs is that they do not provide transparency. With the old paper ballot system, fraud was reportedly widespread, but the reason we know about this fraud is that it was easy to see. Today's EVMs might be counting honestly -- or they might all be rigged -- but there's no way for you, or me, or even the Election Commission to tell the difference, because we can't observe how the votes are counted inside the machines.
Germany and the Netherlands are also modern democracies. They both used electronic voting machines of the same basic type as used in India. In the Netherlands, almost 100 percent of voters used these machines. But when it was discovered that the machines had severe security problems and there was inadequate transparency, the machines were abolished and paper ballots were reintroduced.
Technological advancement is not just about adopting the latest inventions. Over the last decade, science's understanding of how electronic voting security can be compromised has made significant and often startling progress. Innovation also lies in the ability to take a second look and examine whether what seemed like a good idea ten years ago is still a good idea today.
'The EC should stop pretending that EVMs are perfect'
Image: A polling officer arranges EVMs at an election control office in KolkataPhotographs: Parth Sanyal/Reuters
Could you tell us a solution to this problem?
The Election Commission should stop pretending that the EVMs are perfect and start working to create a voting system that provides the transparency voters need in order to have confidence.
Many democracies have adopted and then abandoned electronic voting as science's understanding of the risks progressed. Others have adopted systems that provide transparency and redundant security by combining paper ballots with electronic scanners.
I hope the EC will work closely with India's academic and technical communities -- people like Hari Prasad -- to evaluate the strengths and risks of a range of options and find the best voting system for India.








article